Information is an asset which adds value to any business or organisation and needs to be protected.
ISO 27001 is the internationally recognised leading standard for Information Security (IS) and outlines adoption of an Information Security Management System (ISMS). ISO 27001 acts a framework to follow, it’s not entirely prescriptive, allowing it to be tailored to individual businesses.
In this edition of our newsletter, we will outline the objectives (the ‘what’), benefits (the ‘why’) and approach (the ‘how’) of ISO 27001.
An ISMS is a structured approach for managing and protecting information. There are 3 main objectives for an ISMS:
- Confidentiality – the assurance of data privacy, restricting access so that only authorised persons can view certain information. For example, making sure that only HR executives and line managers can see personnel files.
- Integrity – aims to protect the accuracy and completeness of information, the control for which is making sure only authorised persons can make changes to particular data or information.
- Availability – refers to accessibility; ensuring authorised users have timely and reliable access to any data, information or services they require.
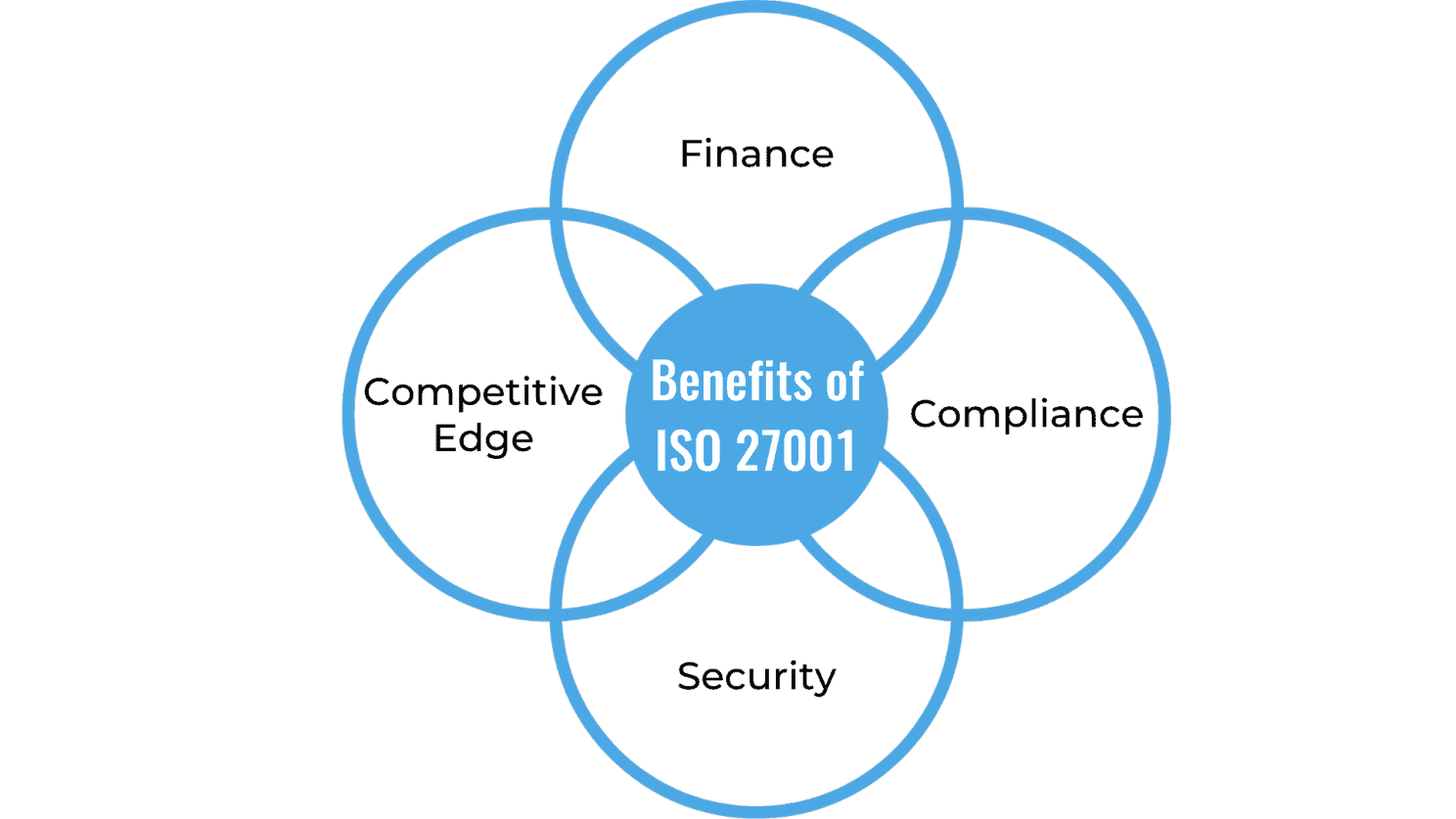
Security measures should be multi-layered to maximise protection, but thankfully it means the benefits stack up too.
ISO 27001 requires an external accreditation for your business to be considered compliant. Displaying this certification can be fiscally beneficial. Certain organisations might choose to partner with you, especially when compared with another who is not certified. Some businesses, especially larger ones, see certifications, such as ISO 27001, as non-negotiable. An ISMS reduces your chances of having a data breach, potentially preventing your business from losing thousands of pounds. Preventing incidents by implementing an ISMS is far cheaper than resolving incidents. So, these protocols can increase your revenue via new business, whilst reducing the likelihood of losing money through a breach.
Following your business’ ISO 27001 scope aligns to legislation and regulatory requirements, such as the Data Protection Act (2018). Developing a culture of security and compliance within your organisation makes the environment more productive; employees won’t have to spend time investigating and fixing breaches, and the management of, and recertification process of ISO 27001 will be far quicker and smoother. It should also save time from reducing audit requests from external partners as you have already verified your commitment to information security.
An ISMS consists of adopting a structured set of policies and procedures which protect a company’s information. Controls are determined by the requirements of interested parties (e.g. client data), risk assessments and management decisions. A PDCA approach is recommended when implementing.
- P – Plan; What & how to do
- D – Do; Implement plan
- C – Check; Assess if objectives are being achieved
- A – Act; Close the gap between Plan & Check phases
IT Security is only 50% of Information Security. HR and Organisational controls are also required, and are just as integral to IS as technical ones.
When implementing ISO 27001, the approach taken is critical to its success. It’s integral the controls are top-down, Board/C-suite level individuals must set the example of following the controls and ensuring everybody else does. Controls should be malleable, and all interested parties can suggest improvements to the ISMS. Policies and procedures outlined by the controls must be continuously followed and reviewed, and if necessary updated and re-implemented.
Best practise for implementing is to assemble a project team. This should start with top-level management who must demonstrate commitment to the ISMS by setting objectives, making decisions and providing all relevant resources. It’s also recommend they appoint individuals to the following roles:
- Project Manager – Responsible for coordinating the team and roll-out
- Project Team – Responsible for documenting, implementing and training others
- Information Security Officer – Responsible for maintaining the ISMS and overseeing improvements (often the same individual as Project Manager)
Documentation is key to Information Security. It’s integral that documentation is viewed as a means of optimising processes and procedures, ensuring ISMS is embedded into company standards; meaning that the documentation is functional, and not merely drafted as a formality to achieve certification. The ISO 27001 standard does dictate certain mandatory documentation, but other items need to be set by top management, tailored to your company or organisation. Strong documentation, created, updated, organised and saved on a frequent basis will solidify your ISMS (and make life easier for your internal Information Security Officer and External auditor!).
“Information Security is of ever-growing importance. Certifications such as ISO 27001 help to protect your business against risk. It’s highly likely that future business insurance premiums will be aligned with the level of IS controls implemented in an organisation”
– Stuart Oldham, CEO Clear Thinking Solutions
Subscribe & share to spread the word on a range of topics covering Cyber Security, Risk & Compliance.
Clear Thinking partner with businesses to provide multi-layered cyber security solutions, including certifications, compliance, disaster recovery and more. Further details can be found here: https://clearthinking.co.uk/cyber-security/